The Role of Data Security in E-Waste Management
There were 2,365 cyberattacks in 2023, affecting over 343,338,964 individuals. About 60% of all data breaches compromise personal data, making it the most frequently affected data category. Additionally, it was found that customers’ personal information was compromised the most, followed by employees’ data.
These days, businesses quickly replace old gadgets with newer models without a second thought. But while their focus may be on upgrading your old devices, they are still holding onto something far more valuable than you realize — your organizational data.
Even after hitting delete or performing a factory reset, sensitive information often lingers in your devices’ memory, waiting to be uncovered. This poses a severe risk when these devices are improperly discarded, leaving your personal or corporate data vulnerable to theft.
In this blog, we will go through the role of data security when disposing of and recycling your organization’s e-waste. Before we begin, let’s explore how your organization’s devices may pose a severe data security risk.
Your Device Still Has Residual Data

One of the most overlooked aspects of e-waste disposal is the residual data that remains on devices long after they are discarded. Data often persists even after deletion attempts, whether on smartphones, laptops, or other digital storage devices. This residual data can include sensitive personal information, financial records, and business data, which can be recovered and used maliciously with the right tools and techniques.
The risk intensifies when devices are improperly discarded or recycled without undergoing a thorough data destruction process. Individuals and organizations must recognize that simply deleting files or formatting drives does not suffice; the data remains vulnerable and recoverable.
What Is Data Security in E-Waste Recycling?
When electronic devices reach the end of their lifecycle, safeguarding data involves more than just hitting ‘delete.’ It requires thorough processes to remove data so it cannot be recovered or misused.
Data security in e-waste recycling refers to ensuring that all personal and corporate information stored on discarded electronic devices is completely and securely erased. This is vital because devices meant to be disposed of can still contain sensitive data, including financial details, personal contacts, business documents, and other private information.
The goal is to protect against data breaches that could occur if sensitive information falls into the wrong hands during the recycling process.
The Role of Data Security in E-Waste Management
The role of data security in e-waste management is extremely critical in today’s data-first world. With annual e-waste generation rising by 2.6 million tons and on track to reach 82 million tons by 2030, integrating data security practices into e-waste disposal processes becomes increasingly evident. Secure e-waste disposal is an environmental responsibility and imperative for data protection.
Ensuring data security in e-waste management involves adopting standardized practices for data destruction before recycling or disposing of electronic devices. This dual focus not only helps safeguard sensitive information but also mitigates the risk of data breaches that can arise from the mishandling of e-waste.
The challenge lies in establishing and enforcing solid protocols that guarantee complete data destruction as part of the e-waste recycling or disposal process. It calls for a concerted effort from individuals, businesses, and recycling companies to prioritize data security as an integral component of e-waste management strategies. By treating data security and e-waste management as complementary processes, we can create a more secure and environmentally responsible approach to handling the growing tide of discarded electronic devices.
What Happens to Data When Devices Stop Working?
When electronic devices stop working, the data stored on them doesn’t simply disappear. Instead, it remains embedded in the device’s storage media, such as hard drives, SSDs, and memory cards. This residual data poses significant risks if incorrectly handled, especially when devices are discarded or recycled.
Even after a device ceases to function, its information—from emails and personal photos to corporate documents and financial records—can still be accessible. Most device failures affect the components needed to operate the device, not the data itself. The data remains intact and can be retrieved using specialized software and tools.
The durability of data means that without proper intervention, it can be exposed during the e-waste recycling process. If devices are simply thrown away or handed over to recyclers without data sanitization, they can fall into the hands of malicious actors. This exposure can lead to identity theft, breaches of confidential corporate information, and other forms of cybercrime.
The Ripple Effect of Improper Device Disposal
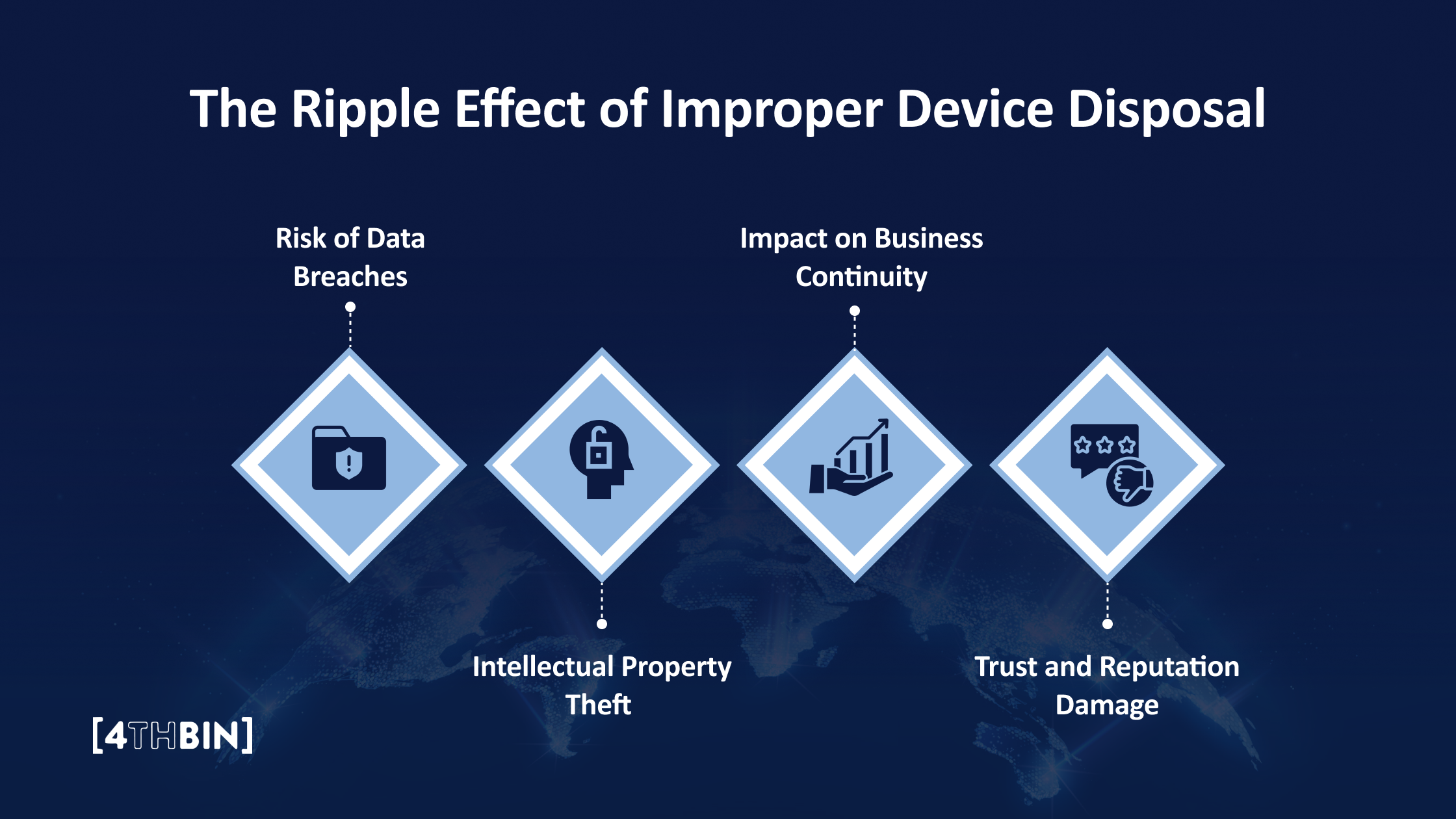
Businesses are particularly vulnerable to data stored on their non-working devices. If not handled securely, disposing of or recycling these devices can lead to significant data breaches that affect the organization’s financial health and reputation.
Risk of Data Breaches
Corporate devices often hold sensitive information, including customer data, proprietary business knowledge, financial records, and employee details. If devices are disposed of without proper data sanitization, unauthorized individuals can recover this information, leading to data breaches. Such breaches cause immediate financial harm and can trigger legal repercussions, including hefty fines and lawsuits under data protection laws.
Intellectual Property Theft
Intellectual property, such as product designs, business strategies, and unique processes, is often stored on electronic devices for businesses. If this information is accessed due to improper disposal practices, it can lead to intellectual property theft, giving competitors an unfair advantage and potentially causing long-term damage to the business.
Impact on Business Continuity
The average cost of a data breach in 2024 is $4.88 million. With businesses losing so much money to a data breach, it may disrupt business operations. The recovery from such an incident requires significant resources and time, during which business efficiency and output can be severely impacted.
Trust and Reputation Damage
One of the most enduring impacts of a data breach is the loss of trust from customers, partners, and stakeholders. The perception that a business cannot safeguard sensitive information may deter potential clients and can tarnish the company’s reputation for years.
How Can Your Business Dispose Its Devices Properly?
Proper electronic device disposal is crucial for environmental sustainability and data security. Here’s how you can ensure that your device is disposed of safely and responsibly:
Data Destruction
To ensure data security, all data on non-working devices must be appropriately destroyed before disposal. This involves using methods like:
- Physical Destruction: This involves mechanically destroying the storage media so that it is no longer usable and data cannot be retrieved. Methods include shredding, crushing, or disintegrating hard drives, SSDs, and other storage devices. Physical destruction is often considered the most foolproof method of data destruction.
- Degaussing: This method uses a high-powered magnet to disrupt the magnetic fields in storage media, effectively erasing its contents. Degaussing is suitable for magnetic storage devices like traditional hard drives but does not work on SSDs and newer media types.
- Software Wiping: Software-based data destruction involves using specialized programs to overwrite existing data with random data multiple times, ensuring the original data is unrecoverable. While effective, this method requires that the device be functional to run the software.
These methods ensure that data cannot be recovered, protect against unauthorized access, and maintain compliance with data protection regulations.
Professional Handling
Given the complexities of securely erasing data, it’s often best to work with experienced e-waste recycling companies, such as 4THBIN, who provide professional data destruction services. These services are equipped with the tools and expertise to handle data destruction efficiently, ensuring that your data privacy is upheld even after your device stops working.
Best Practices for Data Security in E-Waste Management

For businesses, managing e-waste responsibly extends beyond environmental obligations—it is also crucial for safeguarding sensitive information. Here are critical security practices that companies should implement as part of their e-waste management strategy:
Implement a Clear E-Waste Policy
Your organization must develop and enforce a vigorous e-waste policy that is foundational. This policy must clearly outline how to handle old electronic devices, detailing the processes for data destruction, device deactivation, and responsible recycling. It must also ensure that every team member understands their role in securing data throughout the disposal process.
Regularly Update Data Sanitization Protocols
Technology and data storage devices evolve rapidly, as do methods for securely erasing data. Your organization must regularly update data sanitization protocols to ensure that the business is keeping up with the most effective techniques for data destruction, such as software wiping or physical destruction methods.
Train Employees on Secure Data Handling
Employee training is critical in preventing data leaks. Your organization must provide training that covers the importance of data security, the company’s e-waste policy, and steps for securely handling data before device disposal. Regular refreshers will help keep these practices at the top of their minds.
Audit and Monitor E-Waste Disposal
Conduct regular audits of e-waste disposal practices to ensure compliance with both internal policies and external regulations. Monitoring the disposal process helps identify potential security gaps and areas for improvement, ensuring that practices remain up-to-date and effective.
Partner with Reputable E-Waste Recyclers
Choosing the right e-waste recycling partners is essential. Your organization must look for recyclers with certifications like R2 (Responsible Recycling) or e-Stewards, as the EPA defines, indicating compliance with stringent environmental and data security standards. These partnerships help ensure that the physical handling of e-waste aligns with best practices in data security.
Document and Record Disposal Actions
Your business must maintain detailed records of all e-waste disposal actions and provide a clear audit trail that can be invaluable in a data breach investigation. This should include records of what was disposed of, how, when, and by whom, and any certificates of destruction provided by third-party services.
In addition, organizations should regularly review and update their disposal processes to ensure they meet the latest standards and effectively mitigate the risks associated with data loss or leakage.
The Importance of Partnering with Responsible E-Waste Recyclers
Companies must partner with e-waste recyclers who adhere to best practices for recycling and data destruction. Here are a few things your business must consider:
Ensuring Compliance and Protecting Data
Your business must choose e-waste recyclers committed to responsible practices, follow stringent procedures to recycle materials safely, and ensure all data on electronic devices is thoroughly and securely destroyed. This dual approach is essential for businesses to:
- Comply with Legal Standards: Various regulations, such as GDPR in the European Union and HIPAA in the United States, mandate the proper destruction of personal and sensitive data. Partnering with certified e-waste recyclers helps businesses ensure they are in compliance with these laws, avoiding potential fines and legal complications.
- Prevent Data Breaches: Data breaches can lead to significant financial losses and damage to a company’s reputation. By ensuring that all data is destroyed before the recycling process, certified e-waste recyclers help protect the business from the risks associated with data exposure.
Certification and Standards
When selecting an e-waste recycling partner, businesses should look for certifications that indicate compliance with relevant standards and laws. Certifications such as R2 (Responsible Recycling), e-Stewards, and ISO 14001 indicate that a recycler adheres to high standards in environmental management, data destruction, and worker health and safety. These certifications help businesses ensure that their e-waste is handled securely and sustainably.
Building Long-Term Partnerships
Choosing the right e-waste recycling partner is not just a one-time activity but a strategic decision that impacts a business’s sustainability and compliance in the long run. A trustworthy partner helps businesses streamline their e-waste disposal processes, offering peace of mind that all aspects of e-waste management are handled proficiently.
Recycle Your E-Waste & Protect Your Data with 4THBIN

Is your organization struggling to recycle its electronic waste? 4THBIN to the rescue! With over a decade of experience, 4THBIN is a certified and secure e-recycling solution provider to over 10,000 businesses – from Fortune 100 companies to start-ups across the United States.
We believe that no data should be left behind! Backed by our data security expertise, we provide certified data destruction support to today’s top industries. We also help them deliver on their corporate social responsibility commitments by ensuring their e-waste is securely and sustainably recycled.
Secure Your Organizational Data While Recycling Your E-Waste Today!
Contact Us










